
In the ever-changing landscape of technology, companies can no longer rely on a simple plan or checklist when it comes to cybersecurity. The sophistication of attackers and the complexity of today’s digital engagement require companies to constantly evolve their strategies. This article will cover how Nagios Monitoring Solutions can play a critical role in supporting your cybersecurity strategy by predicting, identifying, and preventing security issues.
One of the ways that you can support your cybersecurity strategy is with Nagios XI, our IT infrastructure monitoring solution. XI monitors any mission-critical IT infrastructure components, including applications, devices, Services, operating systems, network protocols, and system metrics, for maximum visibility and awareness. With its flexible architecture and other useful features, XI not only monitors what’s critical but also helps support your cybersecurity in a number of ways.

One of the main ways XI helps your cybersecurity is through its flexibility and extensibility, which can help you comply with any hardened security requirements on any network. XI performs well in the world’s strictest environments, such as top research facilities, multinational corporations, and governments because of these architectural characteristics:
Whether you need to operate on-premises, in a private cloud, a public cloud, or a hybrid scenario, XI has a strategy for security, flexibility, and deployment. It can even operate in various offline environments at no extra cost to provide a higher level of protection from outside attacks. Each XI license also includes a test Instance, which lets you spin up a mirror production Instance, inspect code, and test it against current production security environments.
With XI, you have monitoring freedom, which means that you can monitor any vendor, device, and network with it. This flexibility makes it easier for your organization to take on more complex infrastructure when needed so that every necessary part of your infrastructure is monitored. When you’re able to monitor everything, you have better insight when issues or suspicious activity occur.
With its ability to monitor and alert on nearly anything imaginable, another way you can leverage XI is to detect subtle cues of an attack, like changes in file sizes, a change in the state of a folder, broken scripts, or when a file is updated. To monitor and alert on security threats and malicious attacks, XI includes easy-to-use Configuration Wizards.
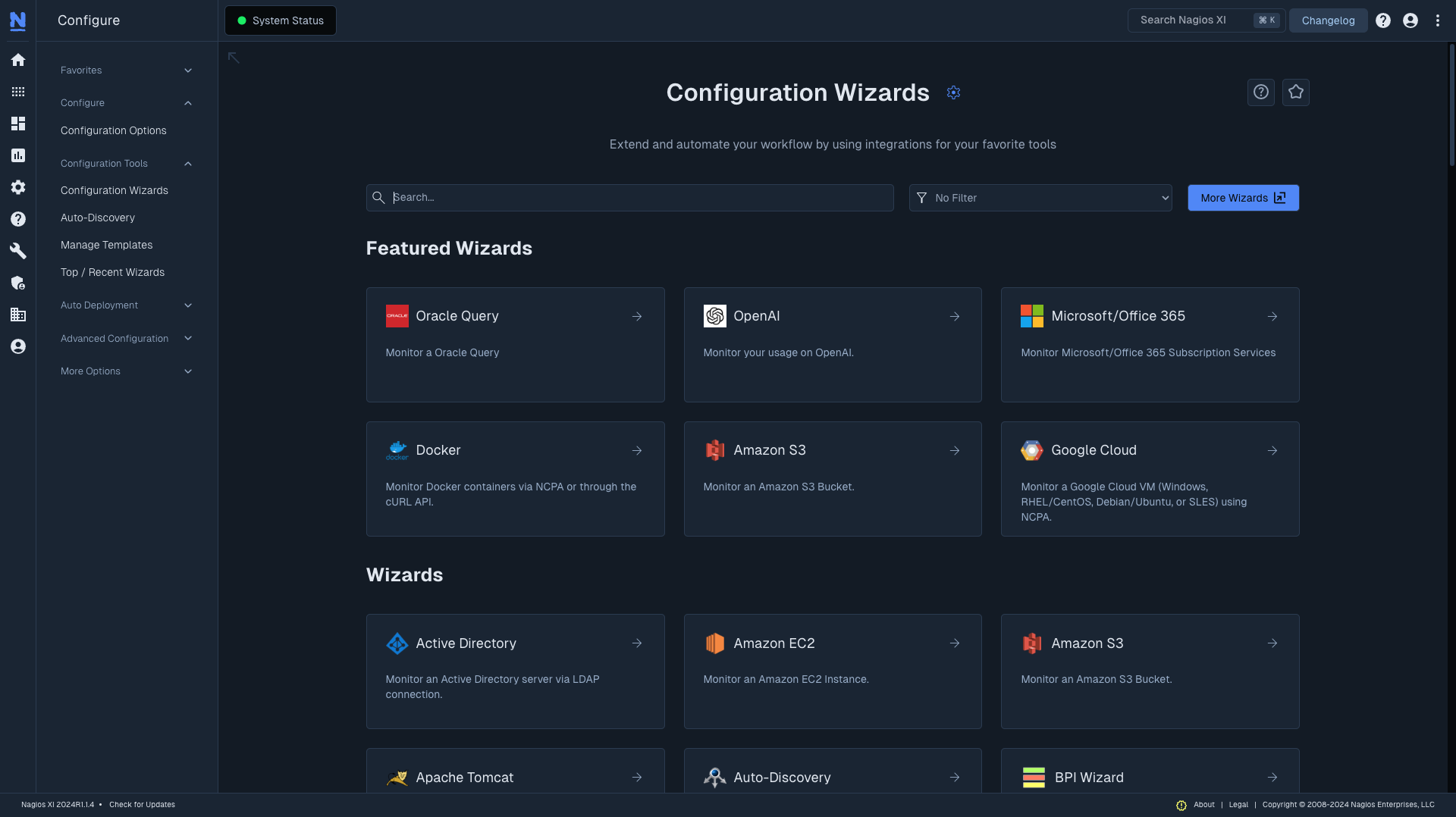
The Website Defacement Wizard, for example, allows organizations to monitor their web resources for hacking attempts by scanning for common words that often appear in pages after a site has been hijacked.
You can track and alert not only on network switch and router interface status but bandwidth and throughput rates with Wizards as well, so system administrators can identify security vulnerabilities on both a physical and virtual level. Additionally, you can use Wizards to monitor operating system error logs and alert appropriate teams when XI identifies failed login attempts or specific intrusion attempts.
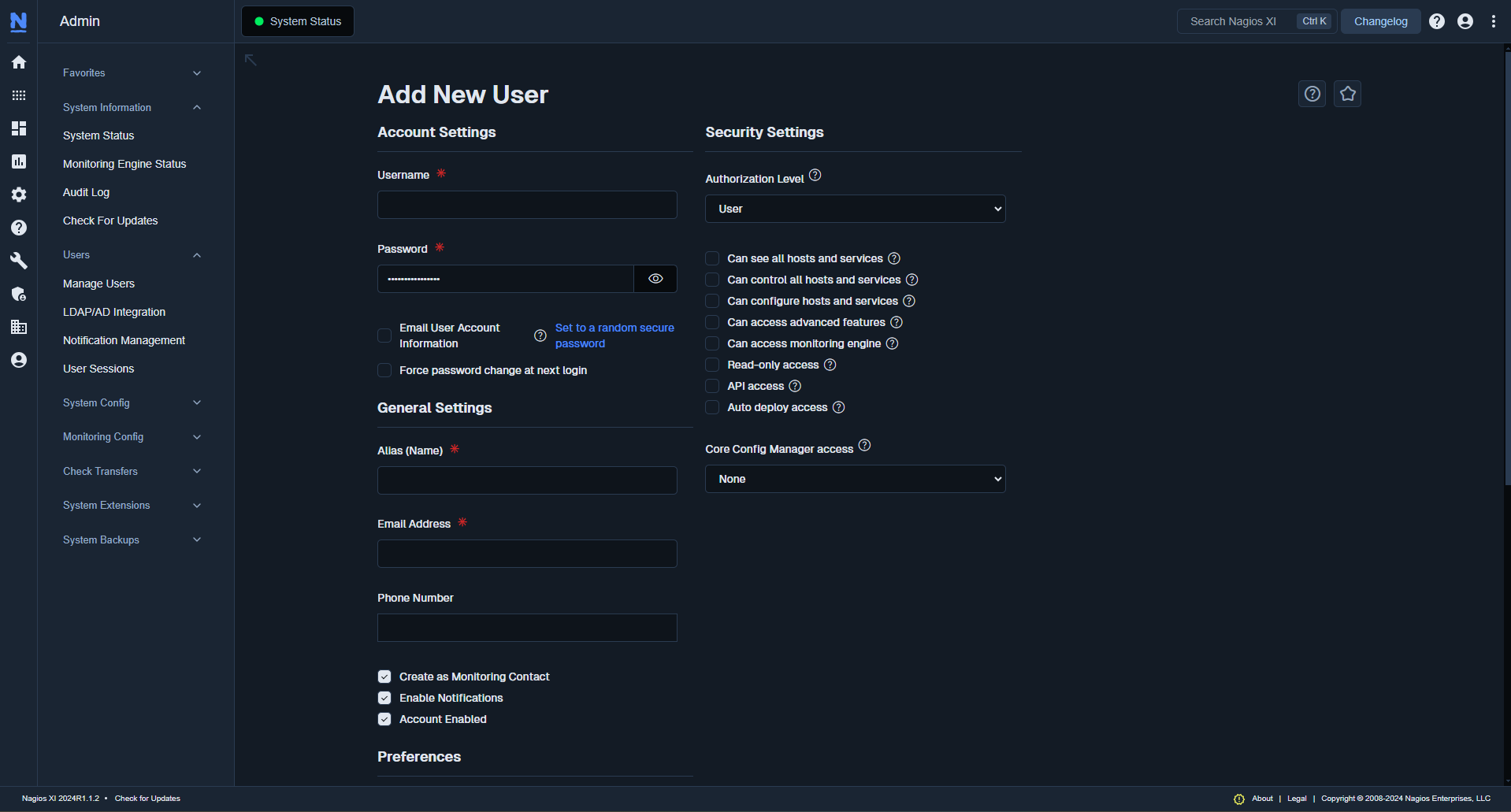
XI features a robust and easy-to-use menu of user and security management options. These options allow system administrators to shut down or control logins, assign specific users access to data based on individual or group properties, define read/write abilities, and even audit exactly what each XI user is doing in real time.
With XI’s user and notification management options, departments and individuals know exactly what their roles are before and during any incidents, cybersecurity-related or otherwise. Each user’s XI account can be customized to display only the information pertinent to their roles, which allows them to focus on the data that matters to decrease downtime.
Notifications and alerts can also be customized based on an organization’s specific needs. XI can alert specific users or groups and then escalate the alerts to other departments based on the severity, time, or location of the incident. Organizing devices and critical business processes in XI is an easy way to quickly identify the root cause and reduce the number of alerts that may otherwise distract from an incident’s resolution.
With these capabilities and XI’s flexible architecture, you’re not only able to monitor when suspicious activity occurs, but your team can also promptly jump into action to resolve the incident quickly before the worst-case scenario has a chance to happen.
Nagios Log Server is an excellent resource for searching your log data, as its ease of use combined with its powerful performance allows organizations to focus on managing security insight. In particular, it allows you to query your log data to quickly audit any system or set up alerts to notify you when potential threats arise.
Log Server is flexible enough to accept any log data from any device capable of sending it, including devices like routers, switches, IoT devices, servers, and workstations. You can filter this data and introduce it into various visual dashboards, in addition to being able to quickly alert the appropriate staff. With these capabilities, Log Server can support three kinds of cybersecurity management strategies: preventative, reactive, and proactive.

The ability to audit, report, alert, and store massive amounts of granular log data is important for any business. These capabilities are why Log Server is a popular solution for businesses that abide by strict compliance regulations. As Log Server monitors your log data, it can help you prevent security issues by producing audit trails in just a few moments with accurate reports and multiple export options. For example, you can narrow and filter user activity logs on a specific workstation from all logs to display data relevant to access and permission attempts.
Log Server can also provide insight into access systems, application servers, financial transactions, gateway data, and many other sources of potential liability or vulnerability with its reporting and alerting capabilities. Since Log Server gives you the ability to create alerts based on custom queries and thresholds, you’re able to stay on top of security and network auditing so you have a better chance of preventing security issues from occurring in the first place.
When you’re unable to fully prevent a cybersecurity issue from arising, Log Server allows you to quickly react to incidents with near-instant alerting based on specific log data. As a result, Log Server immediately notifies you about log data that requires a rapid response to speed up the problem resolution process.
Since we don’t charge you based on the amount of log data you collect with Log Server, you can retain the data you need to with cold storage, which is also helpful for cybersecurity. With this capability, you’re able to look back through your log data to when an intrusion happened, and you can figure out how an intrusion happened.
You can also easily integrate Log Server with XI so security teams can configure actionable scripts called event handlers to perform actions based on log data received. For example, a series of malicious login attempts on a server can trigger an alert as well as an event handler in XI to stop a running Service for a predetermined amount of time. With these two features of Log Server, you’re able to react efficiently when issues arise.
Log Server can also help boost your proactive cybersecurity strategy. The easy-to-use interface of Log Server gives you the power to customize and display various dashboards where log data can be displayed in an easy-to-understand format. You can also use filters to focus on specific metrics inside particularly long strings of data and pinpoint issues before they result in downtime or security vulnerabilities.
Utilizing Nagios Network Analyzer in your IT monitoring setup can also help support your cybersecurity efforts with its network monitoring capabilities. With its advanced alerting and reporting features, you can delve into granular, down-to-the-packet data for comprehensive tracking and analysis. When abnormal activity does occur or bandwidth usage exceeds your specified critical thresholds, Network Analyzer will send you alerts so you can promptly investigate what’s happening. If suspicious activity is happening on your network, Network Analyzer will warn you when you need to take action to prevent a potential issue from compromising your infrastructure.

While Nagios Monitoring Solutions aren’t cybersecurity tools, you can still use them in different ways to support your cybersecurity strategy. XI gives you the customizability and alerting capabilities you need so you can monitor anything that is essential for your business to function securely. Log Server helps protect your infrastructure by allowing you to easily query your log data or set up alerts to notify you when potential threats arise. Network Analyzer also supports cybersecurity by identifying and alerting you when abnormal activity is happening on your network.
Nagios enables you to have some additional help when it comes to identifying potential cybersecurity threats. To test out how Nagios Monitoring Solutions can support your cybersecurity tools, download a free 30-day trial today!
Nagios, the Nagios logo, and Nagios graphics are the servicemarks, trademarks, or registered trademarks owned by Nagios Enterprises. All other servicemarks and trademarks are the property of their respective owner. Website Copyright © 2009-2023 Nagios Enterprises, LLC. All rights reserved.