What You Were Hired For
Keep the infrastructure running
SIEMs analyze security data. The Nagios Security Toolkit delivers the security-relevant visibility foundation that makes it possible.
of SMBs have no in-house security professional. Responsibility lands on existing IT staff.
Untangle SMB IT Security Report
cite lack of time as their top security challenge, ahead of budget or expertise.
DigitalOcean SMB Cybersecurity Report
SMBs are targeted nearly four times more than large organizations.
Verizon DBIR 2025
In many organizations, security did not come with new personnel or tools. It arrived as a result of mandatory audits, cyber insurance obligations, and incident response standards following a failure or near-miss.
IT teams now face more questions without extra time or resources:
Keep the infrastructure running
Auditors require evidence. Logs must be centralized, retained, and searchable when needed.
Insurers require proof of controls like monitoring, logging, and incident response capabilities to assess eligibility and coverage.
Something failed. Now you need to determine what changed, when it happened, and what signals were missed.
Still one person. Same budget. Same expectations.
The Nagios Security Toolkit includes the necessary components needed: Nagios XI for infrastructure monitoring, Network Analyzer for network traffic visibility, and Log Server for centralized log collection. Each tool is deployed independently on your own infrastructure.


Infrastructure Layer
Continuously monitors apps, devices, services, operating systems, network protocols, and key system metrics such as CPU, memory, and disk I/O. Unauthorized devices are revealed as they emerge through XI's Auto-discovery.
Network Traffic Layer
Collects NetFlow, sFlow, J-Flow, and IPFIX data to visualize bandwidth utilization, traffic patterns, and top talkers. Integrated interfaces for intrusion detection, network discovery, and packet-level inspection. Integrates with Nagios XI.
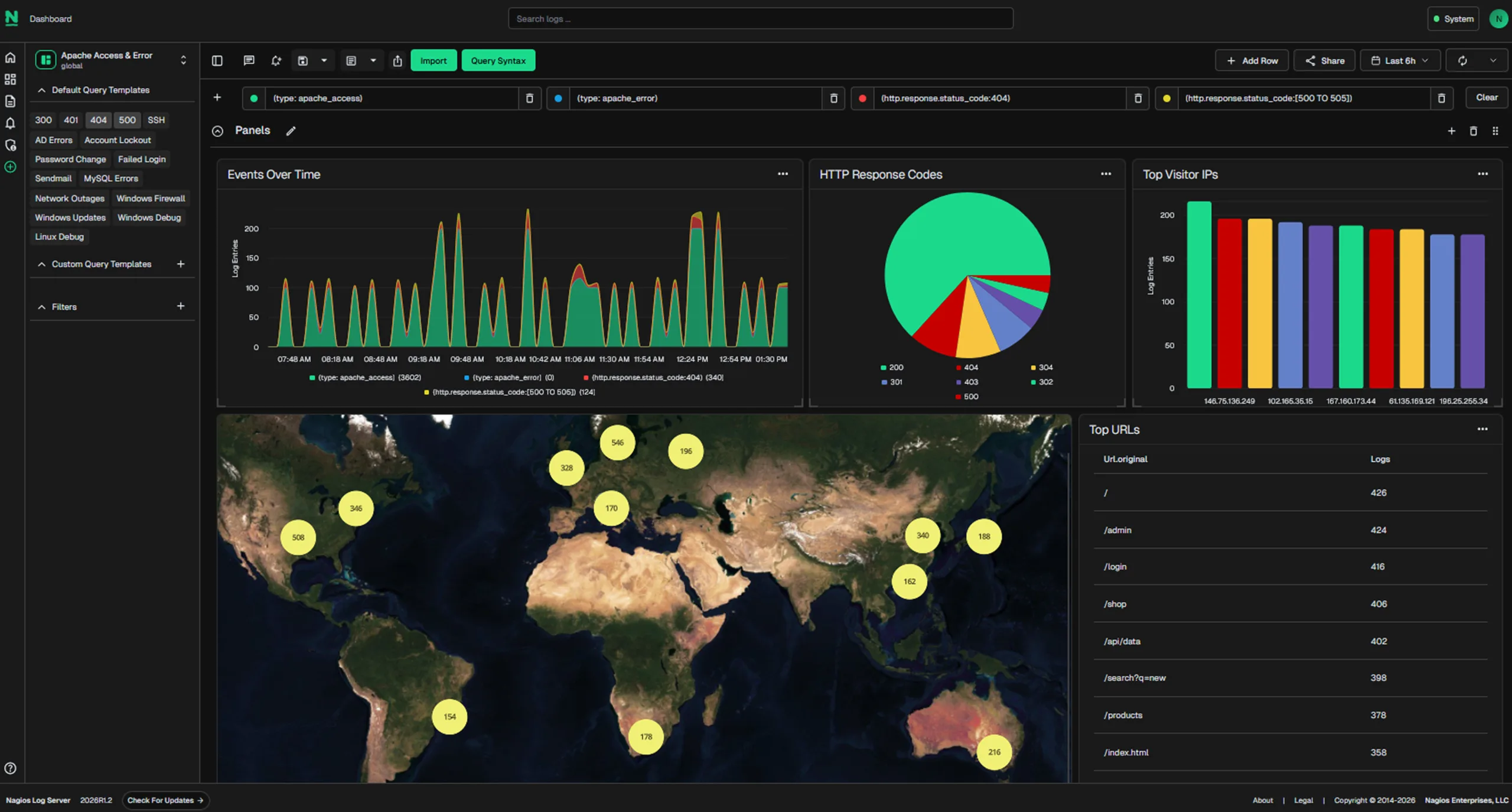
Log Collection Layer
Consolidates Syslog data from servers, firewalls, and network devices into a centralized, searchable repository. Built-in default query for failed login detection. Customizable alert rules on privilege changes and service events.
Infrastructure Layer
Continuously monitors apps, devices, services, operating systems, network protocols, and key system metrics such as CPU, memory, and disk I/O. Unauthorized devices are revealed as they emerge through XI's Auto-discovery.
A SIEM detects, correlates, and investigates incidents using three types of telemetry: device state, flow, and logs. Without all three, coverage gaps reduce detection accuracy and forensic confidence.
Supports detection by monitoring infrastructure state and flagging operational changes or threshold breaches.
Supports correlation rules by adding network flow context to help link traffic behavior with system events.
Supports incident investigation by providing searchable logs to reconstruct timelines and confirm root cause.
Security environments mature in stages, from basic availability checks to full event correlation. Basic monitoring only tells you whether something is up or down. At the other end, a SIEM correlates events across systems using behavioral analytics and threat intelligence.
The Nagios Security Toolkit sits in between, delivering the visibility foundation that makes SIEM adoption work when you’re ready for it.
Is this device up or down?
Powered by the Nagios Security Toolkit. Centralized logs, traffic visibility, and infrastructure monitoring with security-relevant alerting.
Automated correlation, UEBA, threat intelligence. Dedicated analyst required. $50K+ annually.
Walk away knowing exactly what the toolkit does and whether it fits.
Your monitoring data never leaves your network, and your licensing comes with predictable pricing for peace of mind.
Your date stays on your servers. A hard requirement for healthcare, finance, and government compliance — and a sensible default for everyone else.
All Nagios licenses are perpetual and yours to keep. First-year Maintenance & Support is included at no additional cost, with optional annual renewal thereafter.
Your network, your protocols,SNMP, syslog, NetFlow v5, v7, v9, sFlow, J-Flow, and IPFIX. If your devices already send it, Nagios already reads it.
*Maintenance & Support are included free for the first year with all Nagios solutions, with recurring annual renewal pricing after the first year.
No single tool can make an organization compliant.
Compliance is an organizational initiative. The Nagios Security Toolkit addresses particular technical control requirements, such as infrastructure-level logging, network monitoring, and traffic visibility features that help support your overall compliance posture.
Establish the foundation SIEMs depend on with centralized logs, device/service state monitoring, and network traffic analysis.